Introduction to OpenID Connect and OAuth
OpenID Connect and OAuth are the de-facto standards for authentication and authorization in modern applications, yet they involve complex concepts like scopes, claims, and token flows.
his introductory workshop simplifies these fundamentals, giving developers, testers, and architects the skills to implement secure identity solutions. With hands-on exercises and practical insights, participants will gain a solid foundation to prevent vulnerabilities and work confidently with systems like Duende IdentityServer, Keycloak, and Entra ID.
What you will learn
- Authentication vs. authorization
- How OAuth 2.x and OpenID Connect work
- Fundamental concepts
- How a client authenticates against an authorization server
- How to retrieve and consume JWT tokens
- How OpenID Connect fits into your architecture
- How the tokens are secured and managed
This course includes many hands-on exercises that will help you understand how the protocol works under the hood.
After this course, we recommend taking the Web Security Fundamentals workshop. Understanding core web security concepts is crucial when implementing and working with authentication solutions.
For a detailed introduction to OpenID Connect, visit OpenID Connect for Developers, a guide designed to complement this workshop with practical insights and core concepts.
Who Is This For?
This course is designed for both new and experienced developers and architects seeking to understand the fundamentals of application security using OAuth2 and OpenID Connect. With a focus on the core standards and protocols rather than a specific implementation or programming language, it’s the perfect fit regardless of whether you use Duende IdentityServer, Entra ID (AzureAD), KeyCloak, or any other authorization service.
Prerequisites
You should have a good understanding of the following:
- The HTTP(s) protocol (including methods, headers, and cookies…)
- How the web works in general.
- Familiar with REST APIs and JSON
- Some experience in developing backend web solutions
OpenID Connect and OAuth agenda
In this workshop, we will cover the following:
- Introduction
- Authentication vs. Authorization
- Our challenges
- OAuth versions
- OAuth vs. OpenID Connect
- Token Service
- Authorization Server
- Relying party
- Token types
- Bearer token
- Server implementations
- Identity architecture
- Service endpoints
- The discovery document
- Implicit flow
- How does this flow work
- Why it is no longer a recommended flow
- JWT tokens
- ID and access tokens
- JSON Web Tokens
- JWT access tokens
- Claims and scopes
- What are claims?
- Claim types
- Scopes
- User consent
- Securing the tokens
- Unsecure tokens
- Signed tokens
- Signature algorithms
- Private/public keys
- Encrypted tokens
- Authorization Code Flow
- Public vs. private clients
- Front vs. back-channel
- Getting the tokens
- Refresh tokens
- One-time refresh tokens
- Using the refresh token
- Token introspection
- Client Credentials flow
- Proof Key for Code Exchange (PKCE)
- State and Nonce
- Single sign-on and sign-out
- Backend for Frontend (BFF)
- OAuth 2.1
- And much more…
Introduction to
OIDC and OAuth
Article SKU
T340
Duration
1 day
Level
Beginner
Language
English, Swedish
Price
Contact me for a price enquiry or to submit interest.
Learn how to Build Secure and Customized OIDC Flows
This workshop equips you with a solid understanding of the core principles of OpenID Connect (OIDC) and how it integrates with OAuth 2.x to enable secure authentication and authorization. You’ll explore the key differences between authentication and authorization, how tokens work, and the role of claims and scopes in securing identity flows. By diving into the mechanics of client-server interactions, you’ll gain the skills to authenticate clients against an authorization server and retrieve, validate, and consume JWT tokens effectively.
Through hands-on exercises and practical insights, you’ll also learn how to secure tokens with signing and encryption, implement advanced flows like Authorization Code Flow with PKCE, and configure Single Sign-On (SSO) and Single Sign-Out. By the end of this workshop, you’ll understand how OpenID Connect fits into modern application architectures and be prepared to design scalable, secure identity solutions for real-world projects.


Book A Free Workshop
Experience is the key to a great workshop! Why not put me to the test? Get in touch for a free 30-45 minute workshop tailored to the topics and challenges you’re facing, delivered either in-person or remotely.
- tore@tn-data.se
- +46 708 166856
Why take the OIDC and OAuth workshop?
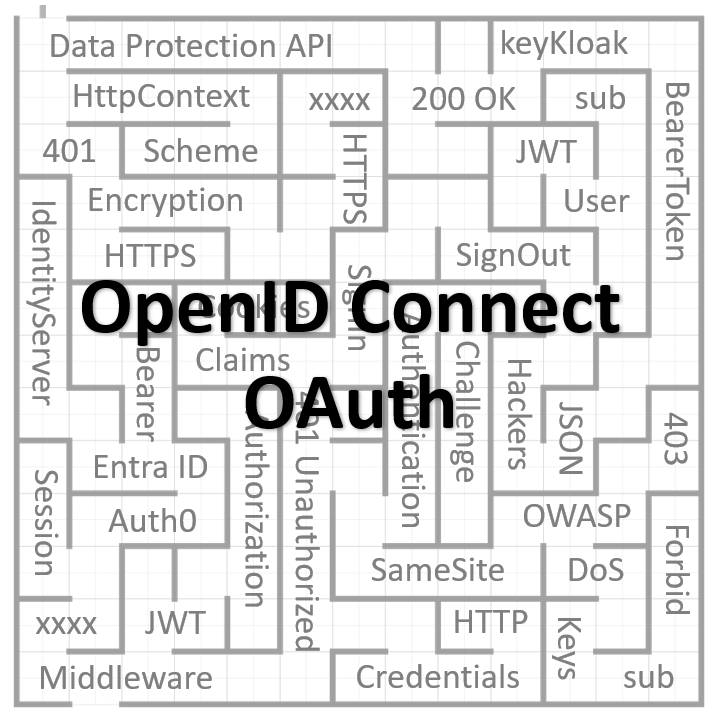
As systems increasingly rely on OpenID Connect (OIDC) for authentication, developers, testers, and architects need a solid understanding of its core principles. Newcomers to OIDC often find it challenging, as it involves many moving parts, specifications, and concepts as shown below:
Without a clear grasp of these fundamentals, implementations risk introducing security vulnerabilities. Real-world examples show the impact of such flaws:
- Critical vulnerabilities in JSON Web Token libraries
- Severe Security Flaw Found in “jsonwebtoken” Library Used by 22,000+ Projects
- Zero-day in Sign in with Apple
- Critical OAuth Flaws Uncovered in Grammarly, Vidio, and Bukalapak Platforms
Understanding the core principals of OpenID Connect and OAuth is a core skill and the Introduction to OpenID Connect and OAuth workshop will give you a good starting point in your journey into the world of OIDC.
OIDC and OAuth Workshop FAQ
Here are answers to common frequently asked questions about this workshop.
Do I need to install any software on my computer?
No, there’s no need to install any software. Each participant in this workshop will receive access to a Windows-based virtual machine, where all hands-on exercises will take place. You’ll only need to connect to this virtual machine via remote desktop, making it easy to participate without concerns about local restrictions on your computer or network. This setup allows us to create a consistent, ready-to-use environment for all participants.
How can I test if I can connect to the virtual machine?
If you’d like to verify your connection capabilities before the workshop, please contact us, and we’ll provide a test machine for you to try connecting to. Testing this in advance is recommended to ensure that your network allows outgoing remote desktop connections, so we don’t encounter any connectivity issues when the workshop starts.
What if I have a Mac or Linux computer?
If you’re using a Mac or Linux computer, you’ll need to be familiar with connecting to a Windows-based virtual machine via remote desktop before the workshop. Here are some recommended resources to help you set up a remote desktop connection:
Remmina – Linux remote desktop client.
How to Use Remote Desktop in Linux or macOS to Connect to Windows 10.
Microsoft Remote Desktop – Mac App Store
Setting up ahead of time will ensure a smooth experience when connecting to the virtual machine during the workshop. Please note that we are unable to provide technical support for Mac or Linux setups.
Is this course made for a specific authorization server?
No, this is a general workshop suitable for any OpenID Connect server, including Duende IdentityServer, KeyCloak, or EntraID. The course focuses on OAuth and OpenID Connect principles, not a specific service.
What do I need to do before the workshop?
Feel free to send the instructor any specific questions you’d like covered in the class. Be sure to read the welcome letter you’ll receive before the workshop. A large monitor is recommended so that you can view the exercise document (provided as a PDF) alongside the remote machine while doing the exercises.
Is there any programming involved?
No, this workshop does not require programming. The focus is on understanding OpenID Connect and OAuth concepts, without tying them to a specific platform, implementation, or language.
What is included?
When taking the Introduction to OpenID Connect and OAuth workshop, you’ll receive:
- Comprehensive Course Material:
Created by the instructor, the material is regularly updated to reflect the latest practices and standards. - Hands-On Exercises:
Engage in practical exercises on a dedicated authorization server, learning core flows and protocols at an HTTP level. - Ongoing Support:
During and after the workshop, access a private chat for additional resources, questions, and updates. - Workshop Materials:
Receive a PDF of the presentation and exercises; onsite participants get printed copies of the exercises on paper. - Live and Interactive Sessions:
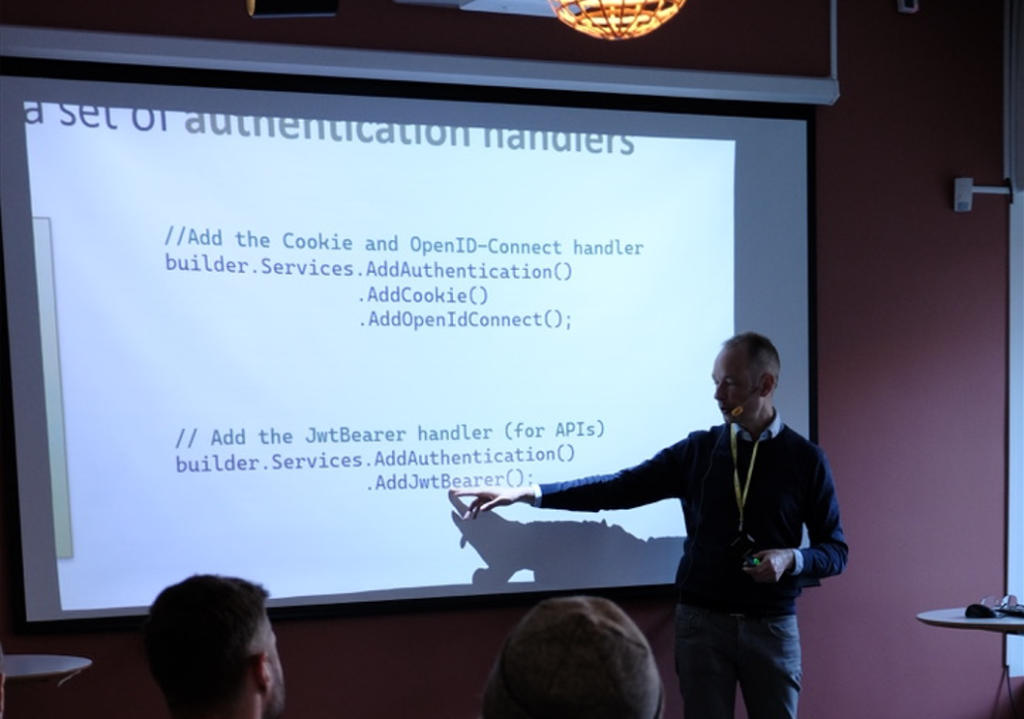
Ask questions in real-time via chat or audio and get immediate clarifications. Includes live demonstrations by the instructor.
OpenID Connect and OAuth Resources
I frequently write about OpenID Connect and authentication on my blog. Some of the posts relevant to this course are:
- Demystifying OpenID Connect’s State and Nonce Parameters in ASP.NET Core
- Debugging JwtBearer Claim Problems in ASP.NET Core
- Debugging OpenID Connect Claim Problems in ASP.NET Core
- Debugging cookie problems in ASP.NET Core
After the Workshop
Following the workshop, I offer ongoing support to help you apply what you’ve learned:
- OpenID Connect and OAuth Consulting:
Personalized guidance for integrating secure authentication and authorization in your projects. - Duende IdentityServer Implementation:
Coaching, setup, configuration, and customization support tailored to teams using Duende IdentityServer. - Architecture Review and Coaching:
Need an architecture review or focused coaching? I offer assessments and advice to optimize security and performance. - Team Training & Workshops:
Custom sessions to strengthen your team’s understanding of OpenID Connect, OAuth, and essential security practices.
Meet Your Instructor
Hello! I’m Tore Nestenius, a senior software developer, trainer, and consultant with deep experience in security, authentication, OpenID Connect, and OAuth. I focus on helping developers and teams understand secure identity solutions in a straightforward and practical way.
Why I’m an expert in this field:
- Helping others
I’ve written over 1,000 Stack Overflow answers, mostly on authentication, IdentityServer, and OpenID Connect. - Duende IdentityServer
I provide training workshops and consulting services on Duende IdentityServer, a widely-used OpenID Connect and OAuth 2.0 framework. - Sharing knowledge
My blog covers OpenID Connect, OAuth, and related security practices. - Frequent speaker
I regularly present on security and authentication at conferences and user group meetups.
Follow me
Connect with me on LinkedIn and subscribe to my monthly newsletter to stay updated on my latest blog posts, upcoming presentations, webinars, and more.
Training FAQs
Do you provide both on-site and remote training classes?
Yes, we provide both types of training.
Do you provide training in both Swedish and English?
Yes, both options are available. All our course materials are in English and we can teach the class in either Swedish or English.
Do you do half-day training?
When we run on-site, we usually do full-day classes. For remote training, we can provide options for both half and full days.
Do you do webinars and shorter talks?
Yes, please visit our Talks page for more details.
Do you provide customized courses?
Yes we do that. Contact me for more information.